Earlier this week, Microsoft released Security Advisory (2953095): Vulnerability in Microsoft Word Could Allow Remote Code Execution
The problem: when Microsoft Word parses specially crafted RTF-formatted data, it can cause system memory to become corrupted and an attacker could execute arbitrary code as a result.
This vulnerability could be exploited through Microsoft Outlook only when Microsoft Word is the email viewer, and Word is the only email editor/viewer in Outlook 2007, 2010, and 2013. An attacker could also exploit the vulnerability by sending a specially crafted RTF email message to the user.
The recommended solutions are to disable RTF document support in Word; if enabled, disable the option to open RTF messages in Word if using older versions of Outlook; and enable “read as plain text” in Outlook.
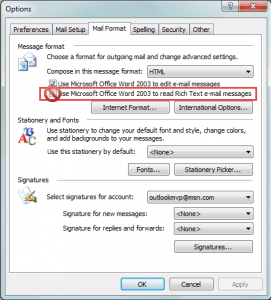
To check and disable RTF settings in Outlook 2003 and older: Open Tools, Options, Mail Format tab. The option to Use Microsoft Office Word to read Rich Text e-mail messages should be unchecked.
While you are unable to disable Word as the email reader in Outlook 2007, 2010, and 2013, you can configure Outlook to read all mail using plain text format by default. Or use a macro to convert RTF formatted messages to plain text format.
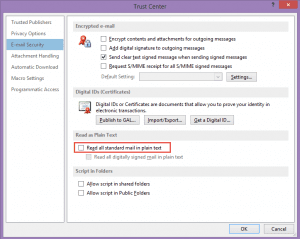
In Outlook 2010/2013, the Read all standard mail in plain text setting is in File, Options, Trust Center, Email Security.
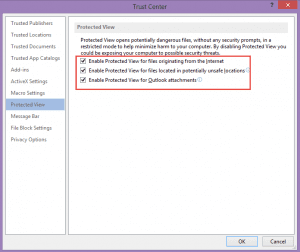
While the options above will protect users from RTF formatted messages, they would still be able to open RTF attachments. To prevent this from happening in Office 2010 or 2013, check Word’s options for Protected View and File Block Settings. In Word’s File, Options, Trust Center, select Protected View. Is Protected View enabled for files originating from the Internet and for Outlook Attachments?
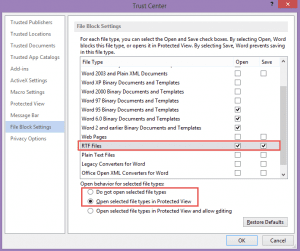
Select File Block Settings and adjust the settings so RTF messages are opened in Protected View or blocked from opening.
File Block Settings and Protected View can be controlled using Group Policy for Office 2007, 2010, and 2013. Sites still using Office 2003 can set a registry key to block RTF documents. Note that all current security updates must be installed for the key to work.
Outlook 2003 registry key
HKEY_CURRENT_USER\Software\Microsoft\Office\11.0\Word\Security\FileOpenBlock
DWORD: RtfFiles
Value: 1
If you don't want to edit the registry yourself, I have a ready to use reg file here: RtfFiles - Outlook 2003
With File Block set, users who have not configured a special exempt directory or have not moved files to a trusted location will be unable to open RTF files. For more information about the impact of file block setting in Microsoft Office software, see Error message in Office when a file is blocked by registry policy settings.
More Information
Macro to Convert RTF Messages to Plain Text Format
Read Outlook Messages using Plain Text
Microsoft security advisory: Vulnerability in Microsoft Word could allow remote code execution Includes a Mr FixIt to set the File Block Settings for users.