By default, the passwords for Office 365 accounts are set to expire after 90 days. In order to set them to never expire, the PasswordPolicies setting needs to be changed.
You can now turn off password expiration or change the days before expiration in Office 365 via the Office 365 admin web interface.
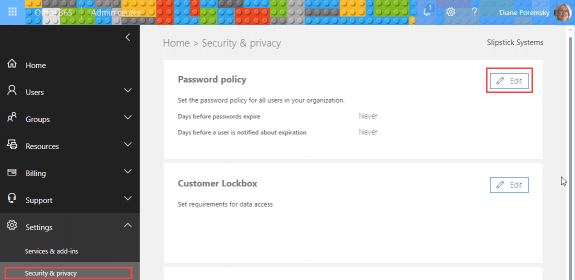
Log into the Office 365 Admin center, expand the Settings menu, select Security & privacy. Click Edit if you need to change any of the settings.
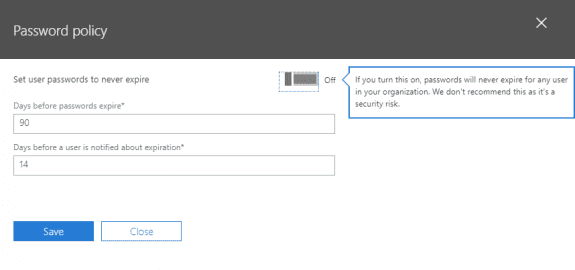
If the password is set to expire, you can change the password age or the length of notification.
Using PowerShell
You can use either the AzureAD or MSOnline module to check password settings.
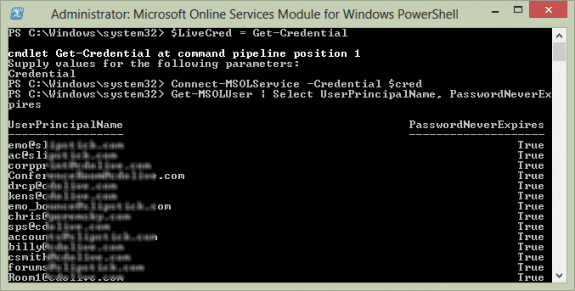
MSOline Module
If you don't have MSOline module installed, open PowerShell using Run as Administrator and use this to install:
Install-Module MSOnline
To connect to it, use this cmdlet, entering your administrator username and password when asked.
Connect-MSOLService
To list all users and see if their password expires, use this cmdlet:
Get-MSOLUser | Select UserPrincipalName, PasswordNeverExpires
Check password settings
To check the PasswordNeverExpires for just one user, use this cmdlet, replacing alias with the user's alias.
Get-MSOLUser -UserPrincipalName alias | Select PasswordNeverExpires
Set passwords to never expire
Use this cmdlet to set all user's passwords to never expire.
Get-MSOLUser | Set-MSOLUser –PasswordNeverExpires $true
To change a single user, use the following command, replacing alias with the user's alias.
Set-MsolUser -UserPrincipalName alias -PasswordNeverExpires $true
To change the passwords to expire, run the cmdlet above but use $false instead of $true.
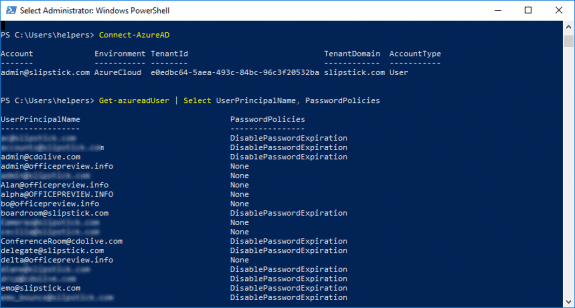
AzureAD Module
If you don't yet have the AzureAd cmdlets installed, open PowerShell using Run as Administrator and use this to install them:
Install-Module AzureAD
With AzureAD installed, run this cmdlet and sign in using the administrator username and password.
Connect-AzureAD
Check password settings
To see the PasswordPolicies setting for all users, run this cmdlet:
Get-AzureADUser | Select UserPrincipalName, PasswordPolicies
To check the PasswordPolicies for just one user, use this cmdlet, replacing alias with the user's alias. (You can use the users email address instead of the alias.)
Get-AzureADUser -SearchString alias | Select UserPrincipalName, PasswordPolicies
Set passwords to never expire
Use this cmdlet to set all user's passwords to never expire.
Get-AzureADUser -All $true | Set-AzureADUser -PasswordPolicies DisablePasswordExpiration
To change a single user, use the following command, replacing alias with the user's alias.
Set-AzureADUser -SearchString alias -PasswordPolicies DisablePasswordExpiration
To get a list of users with password set to never expire:
Get-AzureADUser | ? {$_.PasswordPolicies -match "DisablePasswordExpiration"}
silly question but If I make the changes by setting the password to never expire via MSOL, will this only affect current users but also future users?
It will affect all users, current and new.
Thanks ma'am
Hi, This is awesome information. I'm curious if there is a way to modify this so that a script could be run that turns on PasswordNeverExpires for individual accounts *IF* MFA is active on that account. We have some users that have bought into the MFA and have it active, but some users that do not want an MFA login. The users who have MFA active, should not need to change their primary passwords. I'm hoping to set something up that nightly checks for MFA and then sets passwordtoneverexpire *IF* MFA is active. On this site, you can query for MFA status, but I've got no idea how or if you can create something that queries MFA status and then pipes that into something that would change the passwordneverexpires status.
Thanks
Jeff
The PowerShell module is no longer available :-( I get the message "Microsoft Connect Has Been Retired"
And the new links too confusing to even find the correct download.
Without installing anything (and provided you can log into office 365 with PowerShell), what happens when you enter these two lines;
Connect-MSOLService -Credential $LiveCred
Get-MSOLUser | Select UserPrincipalName, PasswordNeverExpires
It works here and I'm pretty sure I never installed the connector on this computer. (Will test it from a VM next to be sure.)
Apparently, i had the mso stuff installed as it works on my desktop but not on a different computer, even after installing the 2 files in the article footer (the first and last of the 3 still listed)
this worked on the test system:
You need to install the AzureAD stuff - (need to use run as admin when youy open powershell)
Install-Module AzureAD
then this to check the policies
Get-azureadUser | Select UserPrincipalName, PasswordPolicies
and this to set a policy on a user
Set-AzureADUser -ObjectId address -PasswordPolicies DisablePasswordExpiration
https://docs.microsoft.com/en-us/powershell/module/azuread/set-azureaduser?view=azureadps-2.0
The instructions are updated. Thanks for bringing it to my attention.
Sheesh... right after i update the page, i find a new KB article that has this:
Install-Module MSOnline
Connect-MsolService
lol. with those installed the mso code works...
Connect-MSOLService -Credential $LiveCred
Get-MSOLUser | Select UserPrincipalName, PasswordNeverExpires
(guess I will update the page again and add both msol and azuread methods. )
Btw if you are using the Azure AD 2.0 module then here is the updated command:
Set-AzureADUser -ObjectId username@domain.com -PasswordPolicies DisablePasswordExpiration
Even Microsoft's own support page on this from August 2017 is showing the old commands so go figure.
plus you no longer need to use powershell at all, fortunately.
Hello,
Excuse me for correcting you, but if you use $LiveCred = Get-Credential, then the Connect-MSOLService -Credential $cred would as for your credentials again, because the $cred should be $LiveCred, as in the command that defines it... ;)
Heh... no one noticed that mistake until now. Thanks.
Hi Diane,
Is there a way to set individual expiration dates, i.e., standard accounts expire after 90 days, service accounts expire after 6 months?
Thank you in advance
In straight, simple Office 365, no. If you use a hybrid config or Azure AD, possibly - Azure AD apports a fine grained password policy, newer versions of Windows server do. I'm not sure if the basic Azure AD supports the policy or if you need the premium AD offering.
EVERY page I find online has these steps. EVERY time I run "Connect-MSOLService -Credential $cred" I get: The term 'Connect-MSOLService' is not recognized as the name of a cmdlet, function, script file, or operable program
Why does no one explain this!?
Do you have the Online Services Assistant installed? That is needed - you might also need the Online Services Module for Windows PowerShell installed.
Yeah I'm having the same issue and I encounter this a lot when looking for Azure PowerShell commands. Issue is that there is the much more documented older set of commands (you can tell right way if "Msol" is in them) based on the older Azure AD module (installed using "Install-Module -Name MSOnline"). And then the much less documented newer set of commands based on the newer Azure AD 2.0 module (installed using "Install-Module -Name AzureAD"). Which is then also reliant upon using PowerShell 3.0 or above. For example the instructions change right off the bat. You connect to Azure AD using "Connect-AzureAD" instead of "Connect-MSOLService". I don't think you see Msol in any of the newer commands. The newer module is supposed to support more features but its all rather useless if you can never find the commands you need. The "newer" module is over a year old now but you can see here articles written as recently as July are still referencing the older module. That is MS always keeping things interesting for you. So you'll probably have to end up digging through Microsoft's own documentation to find the commands you need or revert to the older module:… Read more »