This content has been archived. It may no longer be relevant.
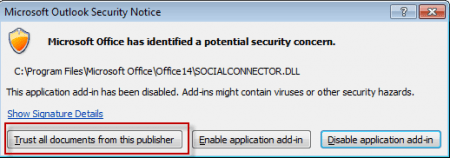
Following the recent update to Outlook's Social Connector, users with the option to "Apply macro security configuration to add-ins" enabled are seeing a security alert from Office. The alert states that Office has identified a potential security threat and lists the Social Connector dll as the culprit. The potential security threat is the result of an invalid digital signature on the socialconnector.dll. (Oops!)
Not everyone will see the problematic certificate. Other files, including Lync's ucaddin.dll may be affected. This will be fixed in future updates but if you can't change the security settings to avoid the alert, you can call Microsoft support and request an updated certificate.
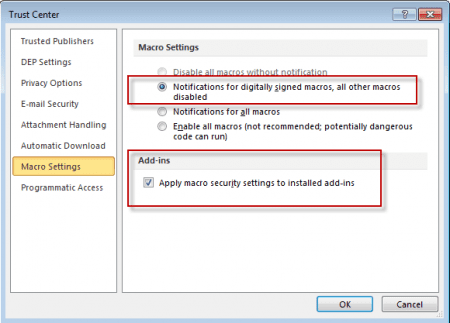
This security warning is triggered by the Add-in security setting in Outlook 2010's File > Options > Trust Center > Macro Settings and is the result of Microsoft using a corrupt certificate to sign the files. This is merely an annoyance for some of those affected. Choosing "Trust all documents from this publisher" to accept and save the certificate will take care of it. However, companies with locked down workstations and a group policy that require a valid signed certificate will not be able to accept the certificate or use the Social Connector until the certificate is fixed. They'll need to choose Disable Add-in each time they start Outlook.
This incident leaves me wondering how easy it would be for someone to install a rogue add-in - the majority of Outlook users did not notice the invalid certificate on the social connector because their security settings allow all add-ins to run. How many of those who saw the warning went ahead and clicked Trust, just because it was (supposedly) a Microsoft add-in?
Known issues with the problematic certificate
- After installing the Outlook 2010 update: April 10, 2012 (KB2553248), there were reports of errors when opening IRM protected messages: "This build of Microsoft Office is unsigned and cannot be trusted by a production Windows Rights Management Services (RMS Server). Before using Information Rights Management (IRM) in this build, specify a test RMS server." In this case, outlook.exe was codesigned with the problematic certificate. The a href="https://support.microsoft.com/kb/2598318">Outlook 2010 April 2012 hotfix package (CU) resolves this issue.
- The most recent version of socialconnector.dll and the Lync ucaddin.dll were also signed using the problematic certificate (note. If Office or Outlook policies or Trust Center settings are configured to Apply macro settings to installed add-ins AND Notifications for digitally signed macros, all other macros disabled, after installing the latest version of the OSC, Outlook displays the error message in the screen shot above.
How to check the certificate an addin was signed with
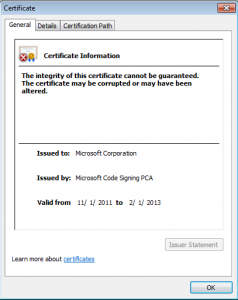 You can check the certificate any application is signed with by right clicking on the file, click Properties. Click on the Digital Signatures tab, select the signer entry, click Details. In the Digital Signature Details window that appears, click View Certificate.
You can check the certificate any application is signed with by right clicking on the file, click Properties. Click on the Digital Signatures tab, select the signer entry, click Details. In the Digital Signature Details window that appears, click View Certificate.
If you want to completely remove the Social Connector, you will need to be logged in as an administrator. Browse to DRIVE:\Program Files (x86)\Microsoft Office\Office14 then locate SOCIALCONNECTOR.DLL and SOCIALPROVIDER.DLL. Rename DLL to InvalidCertificate.
You can disable it completely in Options, Addins and Admins can disable it using group policy.