A user needed help configuring DKIM and DMARC settings in his Office 365 tenant:
I have made the switch to EXCHANGE... But, I cannot find any place in the Office 365 documentation to set up DKIM / DMARC?
The good news: if you have only one custom domain that sends mail set up in your Office 365 tenant, you don’t have to do anything if you added the DNS records for your domain, including the SPF record. (All domains that send mail, including those hosted elsewhere, should have an SPF record).
Office 365 creates a private and public key pair, enables DKIM signing, and configures the Office 365 policy for your custom domain internally and uses it if you don’t have a DKIM record in DNS.
However, you should set up DKIM records if you have more than one domain that sends mails hosted in your tenant, if you are also going to use DMARC, or if you send mail through other hosts, such as a bulk mail service.
DKIM
To set up DKIM, you need to publish two CNAME records for each domain in your tenant.
The format is simple:
CNAME: selector1._domainkey.yourdomain.com Points to: selector1-yourdomain-com._domainkey.tenantname.onmicrosoft.com
Create a second CNAME for selector2, using the same format as above.
CNAME: selector2._domainkey.yourdomain.com Points to: selector2-yourdomain-com._domainkey.tenantname.onmicrosoft.com
Repeat for each domain in your tenant that sends mail. For example, I have slipstick.com and cdolive.com in my tenant and needed to create two CNAME records for each domain name.
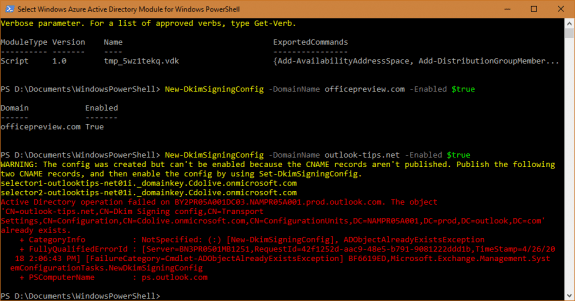
After you create the DNS records, you need to enable DKIM in the Exchange admin or using PowerShell:
New-DkimSigningConfig -DomainName yourdomain.com -Enabled $true
Tip: if the CNAME record isn’t correct or isn’t published, when you run the cmdlet, the failure message will include the correct record to add.
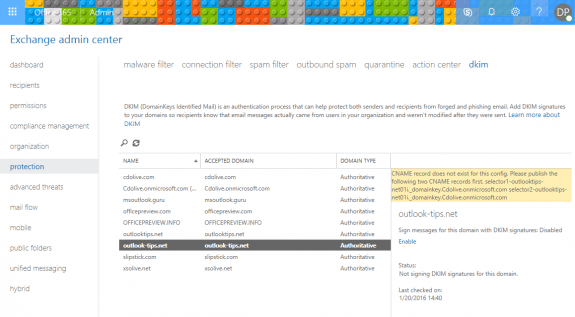
If you prefer changing this in the admin center, log into the Exchange admin center, open the DKIM setting under Protection. Select the domain and click Enable on the right. As with the PowerShell method, if the correct CNAME are not published, an alert will give you the correct names to use.
To verify it is correct, send an email to an Outlook.com or Gmail address and check the header. (Gmail’s Show original command will display the results for SPF, DKIM, and DMARC in a simplified format at the top of the page.)
The header entry will look similar to the following samples. The first example is using the default Office 365 DKIM record:
DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/relaxed;
d=Cdolive.onmicrosoft.com; s=selector1-slipstick-com;
h=From:Date:Subject:Message-ID:Content-Type:MIME-Version;
bh={hash code}; b={signed field}Once the custom DKIM record is created, DKIM in the header looks like this:
DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/relaxed; d= slipstick-com;
s=selector1; h=From:Date:Subject:Message-ID:Content-Type:MIME-Version;
bh={hash code}; b={signed field}
DMARC
To use DMARC you will need to set up SPF and DKIM for your domain (and verify both are correct), before adding the DMARC TXT record to DNS.
Your choices for the policy are none, quarantine or reject. It’s recommended that you start with “none” so you can gauge the impact, especially if you are using third-party mailers to send mail from this domain, before moving to quarantine, or reject.
TXT:_dmarc.yourdomain.com Value: "v=DMARC1; p=quarantine"
To check the results, send a test message to Outlook.com or Gmail address and check the header. Gmail’s Show original option displays the following information:
Message ID <{code}.namprd05.prod.outlook.com>
Created at: {date} (Delivered after 4 seconds)
From: Diane Poremsky <{me}@mydomain.com>
To: "{me}@gmail.com" <{me}@@gmail.com>
Subject: testing
SPF: PASS with IP {address}
DKIM: 'PASS' with domain mydomain.com
DMARC: 'PASS'